February attacks show why we should take cybersecurity seriously
by Diana Gitig, science writer
Rockefeller was attacked some eight billion times last year by hackers. The overwhelming majority of those attempts were thwarted by firewalls, anti-virus software, and other countermeasures maintained by IT’s information security team: the offenders are blocked and we can go about our business.
The situation was different on February 17. Starting around noon that Wednesday, hundreds of Rockefeller University e-mail addresses began receiving particularly crafty emails embedded with malicious code that slipped past the spam filters. The following morning, the university was hit by another malevolent campaign.
The e-mails were relatively sophisticated—each was sent from a unique Yahoo email address using a unique subject line and a unique file attachment—and their payload was potentially disastrous: code that, if executed, could encrypt entire hard drives, making them unreadable.
“It’s known as ransomware,” says Marty Leidner, Rockefeller chief information security officer. “It holds your data hostage until you pay a ransom.” Around the world, between one and five computers per second were infected with this particular ransomware—known as Locky—in mid-February.
An evolving threat
Intellectual property and data are some of the most precious commodities at Rockefeller. The university’s defense mechanisms against cyber attacks rely on recognizing similarities between files, fabricated email addresses, and other factors. But the recent attacks, in which targeted emails were sent to numerous Rockefeller employees, were very difficult to identify. To protect users, Rockefeller’s information security department took the extreme measure of temporarily blocking the offending attachments.
“This was a sophisticated and carefully planned attack, launched by a criminal syndicate with vast expertise and resources,” says Mr. Leidner. “These hackers are not teenagers playing video games in their parents’ basements.” As cyber attacks are becoming increasingly shrewd, the university’s existing defensive tools aren’t as effective as they used to be and user vigilance is more important than ever.
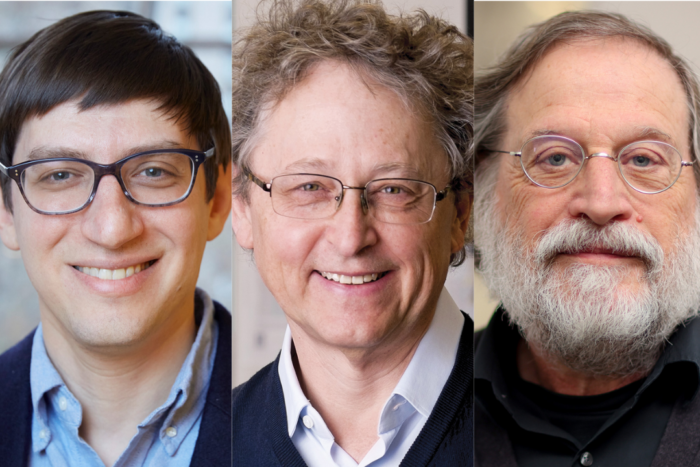
In response to the February 17th attacks, and to underscore the necessity of user awareness, Mr. Leidner and his colleagues Jens Matthes, information security architect, and Bart Mallio, information security intelligence analyst, hosted a question-and-answer session on cyber security for Rockefeller employees, on February 24. Much of the session was devoted to discussing how to dodge attacks and how to be safe online.
Mr. Leidner outlined the warning signs of a phishing email and the preventative steps all internet users should be taking to protect our devices: installing antivirus software, backing up our data, and using strong passwords to make devices, and the data they contain, difficult to access if they are lost or stolen.
What to do—and not to do—to be cyber safe
Ransomware attacks rely on the user’s clicking a link or opening an attachment that then encrypts not only the user’s own files, but any files on a shared server to which the user is connected. Mr. Leidner notes that these emails often have a sense of panic or urgency. In addition, they often use generic salutations, like “Dear customer” or “Dear friend.”
“The emails of February 17 were suspicious in that there was nothing in the body of the message,” he says. “Most real people do not send blank emails. When you receive an email with these features, or with grammatical errors or an unexpected attachment, make sure not to open it or click on anything it contains.”
If in doubt, he says, you may hover over any included link to see the underlying, potentially dangerous web address. Even if it seems to come from a familiar sender, be cautious and call the sender to confirm it is legitimate. If you remain suspicious, forward the email to the IT help desk or call them at x8940.
Antivirus software is essential—and it’s free. Despite a popular misconception, Apple devices as well as PCs need antivirus software. (Just this month, Rockefeller was attacked by a new piece of ransomware called KeRanger, which specifically targets Macs.)
As with vaccines against infectious diseases, protection against computer viruses is a responsibility that must be shared by the whole community, Mr. Leidner says. If one computer without virus protection is compromised, the virus can get onto other campus computers or the central file system to encrypt many people’s files.
“Although protection against malware is prudent and mandatory for all computers connected to the Rockefeller University network, not every user at Rockefeller actually has virus protection on their computer”, Mr. Leidner says. “This is an unnecessary risk and makes us all more vulnerable. My colleagues and I will be happy to assist you if you are unsure whether your computer has current antivirus or backup software installed.”
In the context of ransomware, backups are especially critical as they make it possible to restore data without having to negotiate with the hackers. IT offers a cloud-based backup service called Crashplan for a small fee. In addition to setting it up, users should routinely confirm that the data is in fact being backed up properly, and that it is easily accessible when you need to retrieve it.
Computers, phones, and tablets should be password protected, and the university’s policies state that Rockefeller laptops must be encrypted to protect data on lost or stolen devices. Sensitive files should be encrypted as well, no matter where they reside. Ask IT for help to encrypt your laptop or files, or visit the IT website for instructions on how to save encrypted files.
But what if…?
So, of course you would never open one of these dangerous emails, but it turns out that someone you work with did. How to best contain the damage? Call the IT help desk, then power off the machine and unplug it.